The Buyer's Checklist for API Protection Solutions
Ensure the API protection vendors you evaluate meet the critical criteria your organization requires.
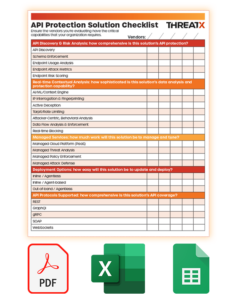 This checklist will help you contextualize your API security vendor evaluation and answer questions like:
This checklist will help you contextualize your API security vendor evaluation and answer questions like:
- how comprehensive is this solution’s API protection?
- does this solution provide in-depth protection across all layer 7 traffic?
- how sophisticated is this solution’s data analysis and protection capability?
- how much work will this solution be to manage and maintain?
- how easy will this solution be to update and deploy?
The checklist is available in three file formats, PDF, Excel Spreadsheet, and Google Sheets.
Get a jump start on column one and request a demo of ThreatX’s API Protection platform today.