Are Your APIs Handling Sensitive Data Securely?
Find out which APIs are managing sensitive data and protect them from threats.
- Detect sensitive data
- Protect high-risk APIs with sensitive data
- Measure and analyze your sensitive data exposure
ThreatX protection ensures your sensitive data stays yours – secured with confidence, not complexity.
How We Help
Sensitive Data Detection
Identify sensitive data in API transactions to prevent exposure
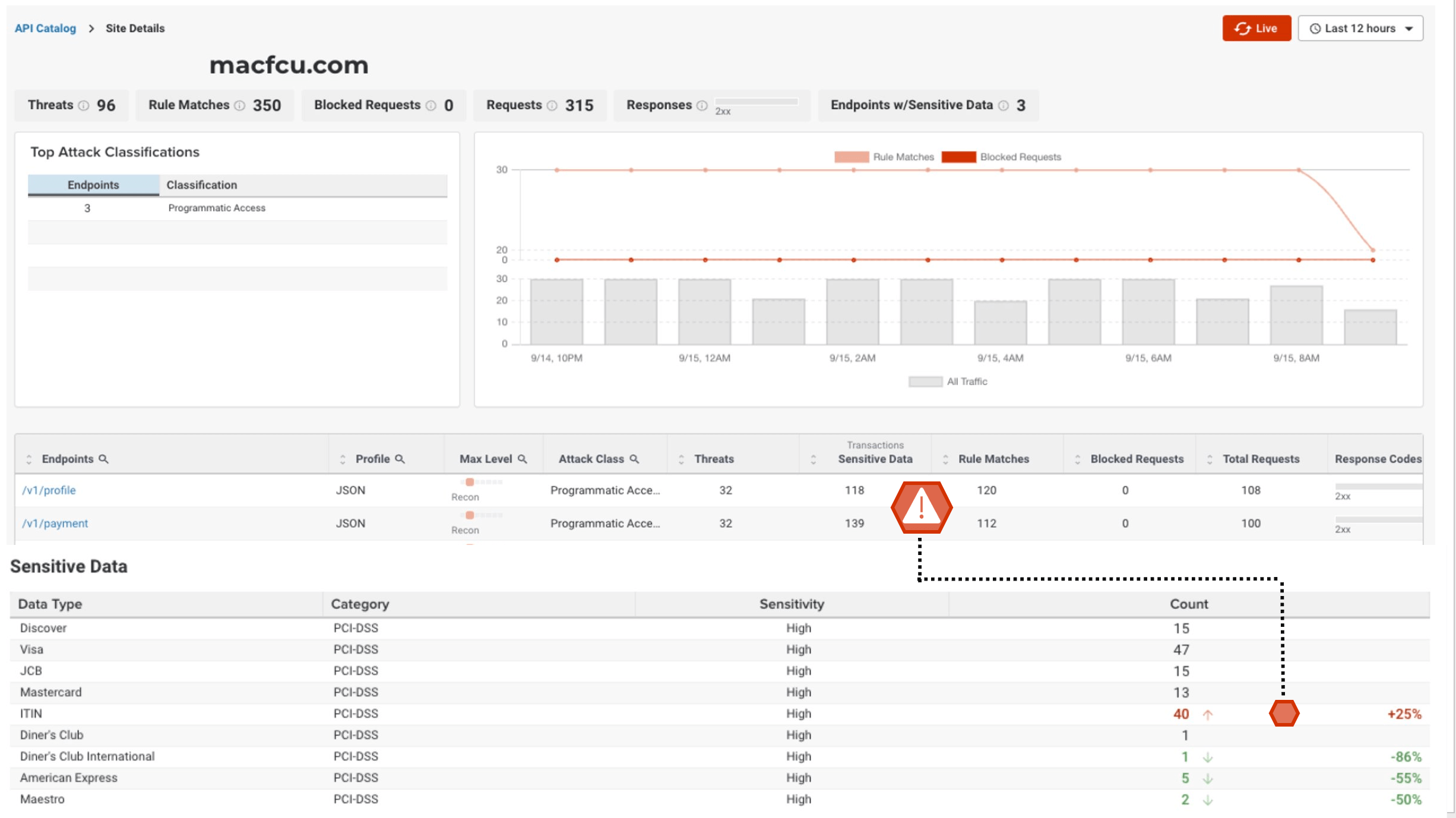
As the ThreatX platform analyzes traffic over time and detects API endpoints, it tracks and visualizes sensitive data, including personal identification, credit card, and authentication data, in the API Catalog dashboard. The platform’s sensitive data detection capabilities enable security teams to easily identify and boost security for high-risk APIs as well as comply with privacy regulations.

Protection for High-Risk APIs With Sensitive Data
Prevent data breaches and comply with privacy regulations with risk-based blocking for APIs with sensitive data
The risk of sensitive data loss is significant and can have serious consequences, such as identity theft, financial losses, damage to a brand’s reputation, and legal and regulatory fines. That’s why ThreatX’s sensitive data exposure protection helps security teams easily identify API transactions that contain sensitive user information and take appropriate action with the platform’s risk-based blocking or alerting – based on your team’s preference.
Sensitive Data Exposure Metrics
Visualize and manage your organization’s high-risk API attack surface to safeguard critical services and data
ThreatX’s API Catalog provides security teams with a comprehensive dashboard for managing APIs and investigating attackers targeting them. Sensitive data metrics and traffic analysis are fully integrated into the API Catalog, offering a visual representation of high-risk APIs within your organization’s attack surface — right down to specific endpoints.

Key Benefits
Secure APIs and applications with Observability, Prevention, and Protection
Eliminate risks without compromising your time or peace of mind.

Easy-to-Use
Experience user-friendly security designed to focus on what matters most. Leverage simplified dashboards so you can effortlessly oversee your API and application’s security posture and risks.
Easy-to-Manage
Get your nights and weekends back with always-active security that ensures your APIs and applications stay safe. Our visionary technology provides continuous protection and prevention without the need for manual intervention. Enjoy peace of mind knowing that your APIs and applications are secure even when you’re off the clock.
Eliminate Risks
ThreatX solutions are always monitoring, assessing, and identifying risks to APIs and applications continuously based on behavior. Our technology learns to recognize threats and vulnerabilities specific to your system, and proactively stops them based on risk level. This ensures your business remains operational and efficient, without interruptions.