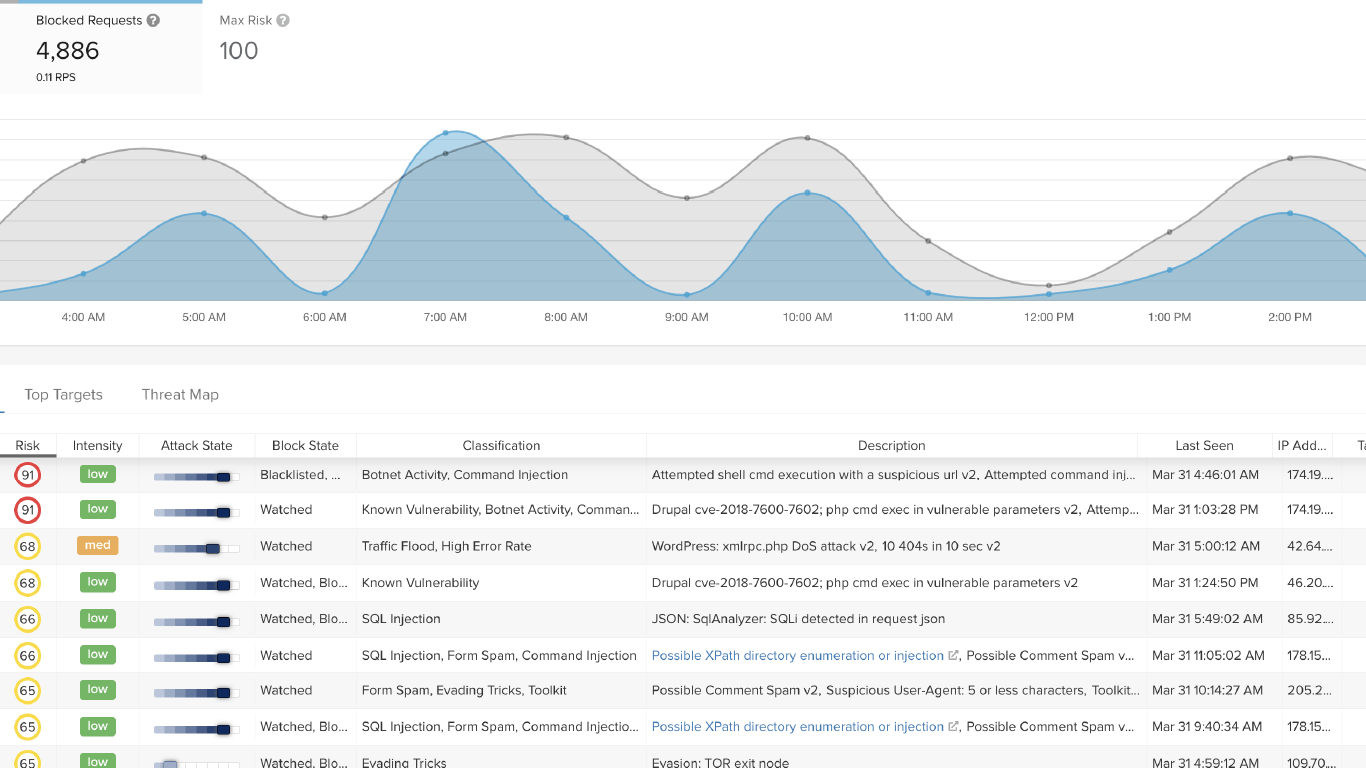
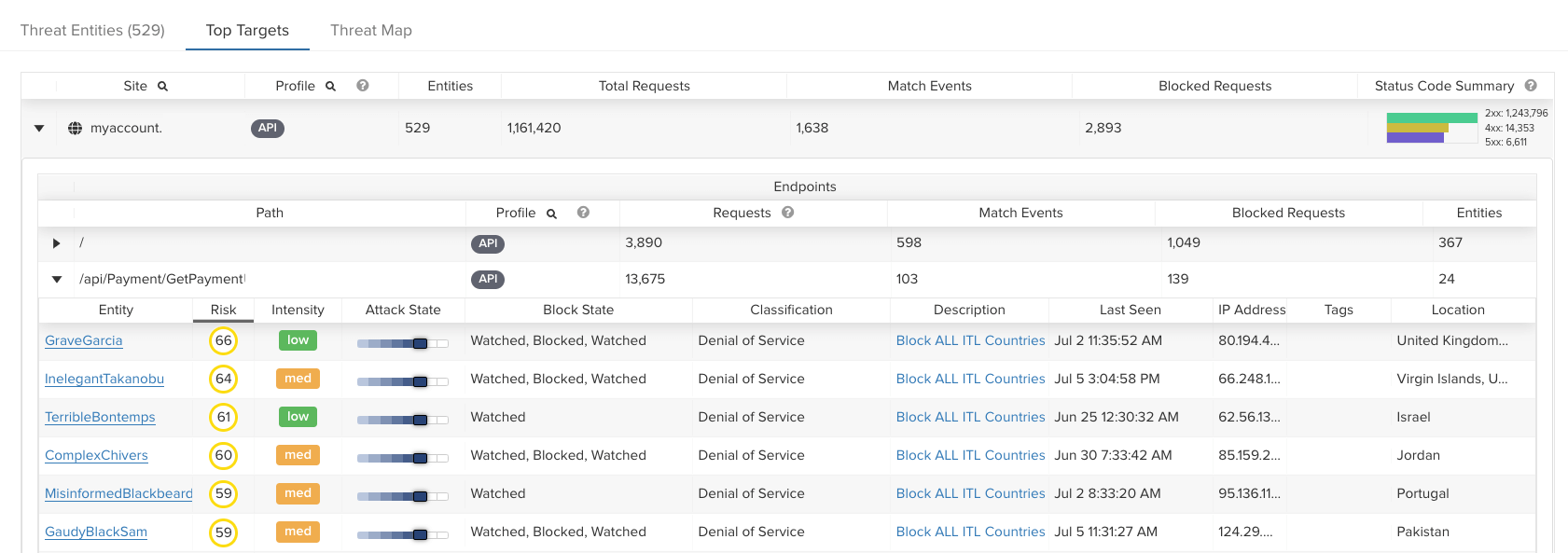
“We had a site that was being target by a bot, attempting to log in with rotating usernames and passwords. However, this threat actor was crafting a properly formed interaction with the API. So, there was nothing malicious. It was using proper user agents and properly formed headers – nothing about it was out of the ordinary. ThreatX’s ability to recognize anomalies that indicate suspicious behavior is game-changing.”
Director of Information Security, Large Marketing Company
Read the full case study