LAST UPDATED August 2, 2021
The ongoing shifts in application technology, cloud migration, and DevOps means it’s imperative to align your web application protection strategy with your dynamic application environment. ThreatX has some powerful new capabilities that take you far beyond the basic protection afforded by legacy WAFs to while minimizing false positives and reducing overhead for optimized security teams. Read on to see what our customers are taking advantage of everyday to protect their apps against top threats:
- Go Beyond Basic Coverage with Advanced SQL & XSS Injection Protection
The OWASP Top 10 has given organizations and security providers insight into the most common threats against web applications for the last decade. And for quite some time, WAFs have hung their hats on the ability to provide basic coverage against those top 10 threats. But that’s just it…the coverage is basic. Legacy WAFs often fail to take into account the growing sophistication and complexity of even the most basic attacks, like SQL Injection. Unlike legacy WAFs, ThreatX built a system that immediately detects and blocks highly-probable SQL and XSS injection attempts using advanced attacker behavior profiling. The key is “highly-probable,” which enables ThreatX to stop a threat before it manifests into a full-blown attack. In addition to blocking the request, the “match event” feeds our analytics engine, continually enhancing threat detection capabilities for all customers.
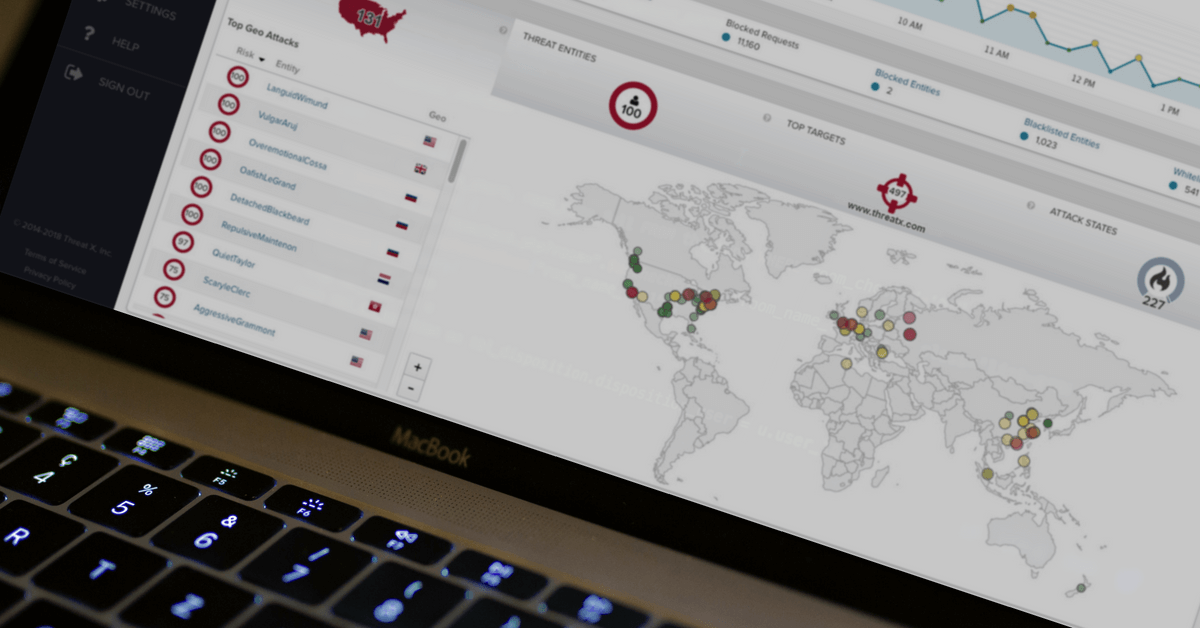
- Stop Advanced Attacks with Multi-IP Entity Tracking & Mitigation
Single entity attackers that may have multiple points of presence via different IP addresses can be one of the trickiest attack techniques to detect. Often times, these attacks are mistaken for a handful of individual threats, which individually may not be enough to elicit a block. When combined however, these attacks signal malicious intent and when left unblocked the results can be disastrous. ThreatX now protects your entire application portfolio against even the most sophisticated multi-IP threats, eliminating the time consuming and inaccurate research and analysis work often required to protect against such attacks.
- Easily Manage Security Data with SIEM & Log Management Integrations The last thing you want your talented security team doing is poring over logs of security event data just to identify trends that could drive optimizations to your security strategies and tools. Their time is better spent on the latter. ThreatX recognizes this and can now forward security-relevant events to your upstream log management and SIEM solutions so you can easily organize high volumes of security data. The forwarded events include match, audit, and sensor. These events are sent in JSON format over a TCP/TLS session, which is compatible with most leading log management and SIEM solutions. Together with the ThreatX WAF, your security team will be enabled to operate more efficiently and make more informed decisions.
The ThreatX team stays at the forefront of WAF innovation – responding both to the direct needs of our customers and to the trends driving the application security space. Attackers are getting smarter – your solution should too. If you’re a customer and have a feature request, reach out to your SOC representative. If you’re not a customer but would like to learn more about ThreatX’s next-generation WAF, join us for an upcoming live demo or contact us.